- >> 情報通信基盤研究部門
-
環境調和型セキュア情報システム研究室
教員

[ 教授 ] 本間 尚文
[ 特任研究員 ] Tasso Élise Léa Marlène
研究室HP
https://www.ecsis.riec.tohoku.ac.jp/index
研究活動
モノのインターネット(Internet of Things)に代表される次世代情報通信基盤は、新たな価値を創出し、豊かな社会をもたらすことが期待されている。一方で、そうした新しいICTの利用形態におけるセキュリティが、既存技術の単純な延長により達成されるとは限らない。データ詐称によるアプリケーションの無価値化や工場の重要制御情報の改竄といった、想定される新たな脅威は枚挙にいとまがない。本研究室では、将来のサービスやテクノロジを誰もが安心して利用でき、その恩恵を安全に享受できる情報通信基盤の構築を目指して、次世代の情報セキュリティシステムの基礎理論とその実装技術を探求している。
環境調和型セキュア情報システム研究分野|本間教授
研究テーマ
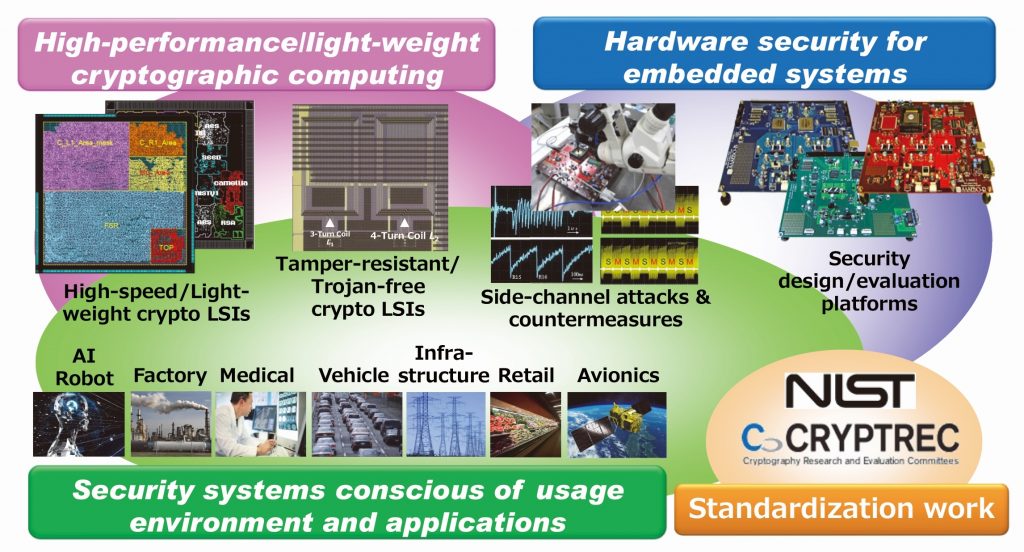
- 高性能・軽量セキュリティコンピューティング
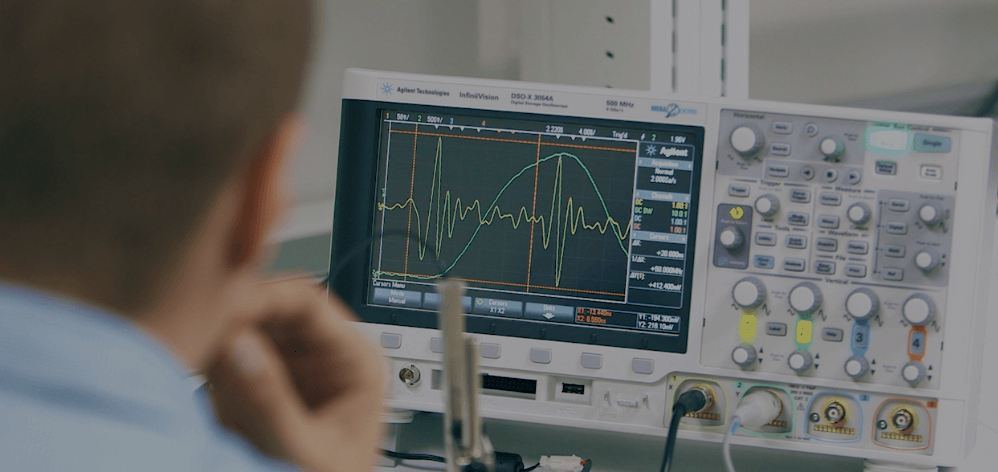
- 組込みシステムのハードウェアセキュリティ
- 使用環境や応用を考慮したセキュリティシステム
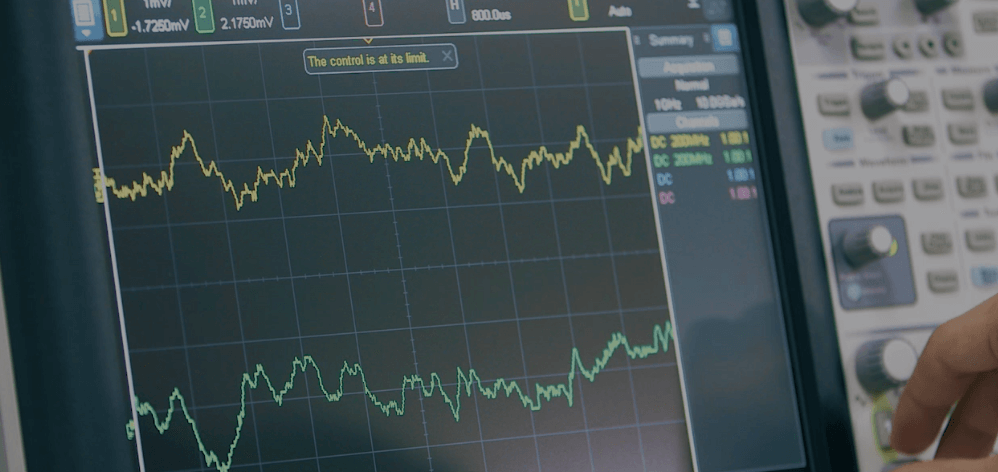
- 電磁情報セキュリティの理論と応用
本研究では、ネットワークやソフトウェアのセキュリティの確保のみならず、膨大かつ多様な情報発生源(センサ端末などのデバイスハードウェア)のレベルから安全性・信頼性を担保するセキュア情報通信システムの構築技術を開発している。また、組込みシステムのセキュリティは同システムが置かれた環境や用途に大きく左右されることから、様々な環境や応用におけるシステムのセキュリティ設計・解析・評価技術の開拓も並行して行っている。さらに、上記の研究開発から得られた成果の積極的な社会実装に挑戦するとともに、各種標準化検討委員会での活動を通して標準化を推進している。